G Wireless Network Secure Data Sharing: A Comprehensive Guide
Introduction
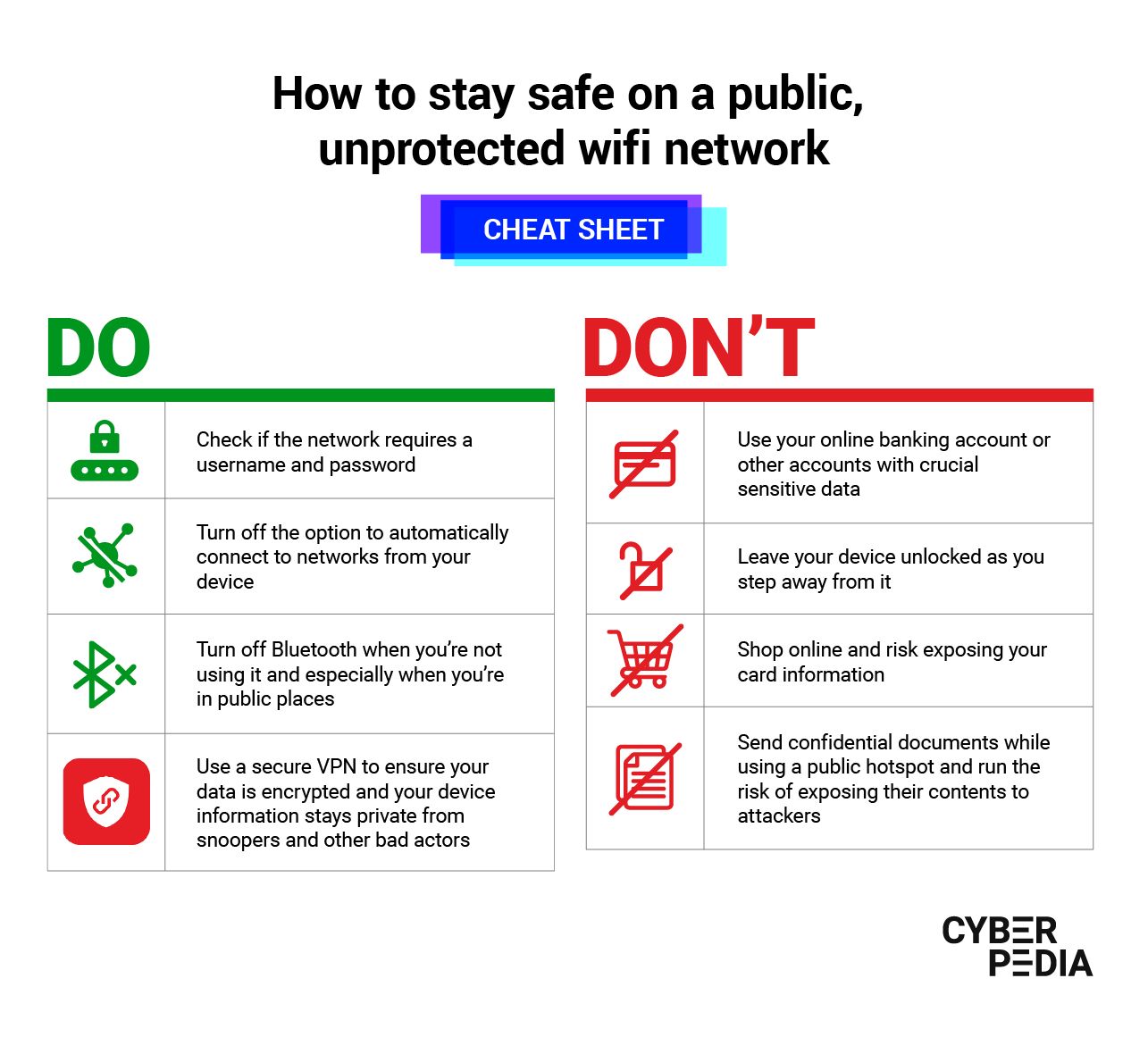
The widespread adoption of wireless networks has revolutionized the way we communicate, work, and live. However, with the convenience of wireless connectivity comes the risk of data breaches and unauthorized access to sensitive information. In this article, we will delve into the world of G wireless network secure data sharing, exploring the best practices, technologies, and protocols that can help protect your network and keep your data safe.The Importance of Wireless Network Security

Key Technologies and Protocols for Secure Data Sharing
Several technologies and protocols play a crucial role in securing G wireless network data sharing. Some of the most important ones include:- Advanced Encryption Standard (AES): AES is a widely used encryption algorithm that provides strong protection for data transmitted over wireless networks.
- Wi-Fi Protected Access 2 (WPA2): WPA2 is a security protocol that uses AES encryption to protect data transmitted over Wi-Fi networks.
- Wireless Protected Access 3 (WPA3): WPA3 is the latest security protocol that provides enhanced protection for data transmitted over Wi-Fi networks, including individualized data encryption and optional secure key exchange.
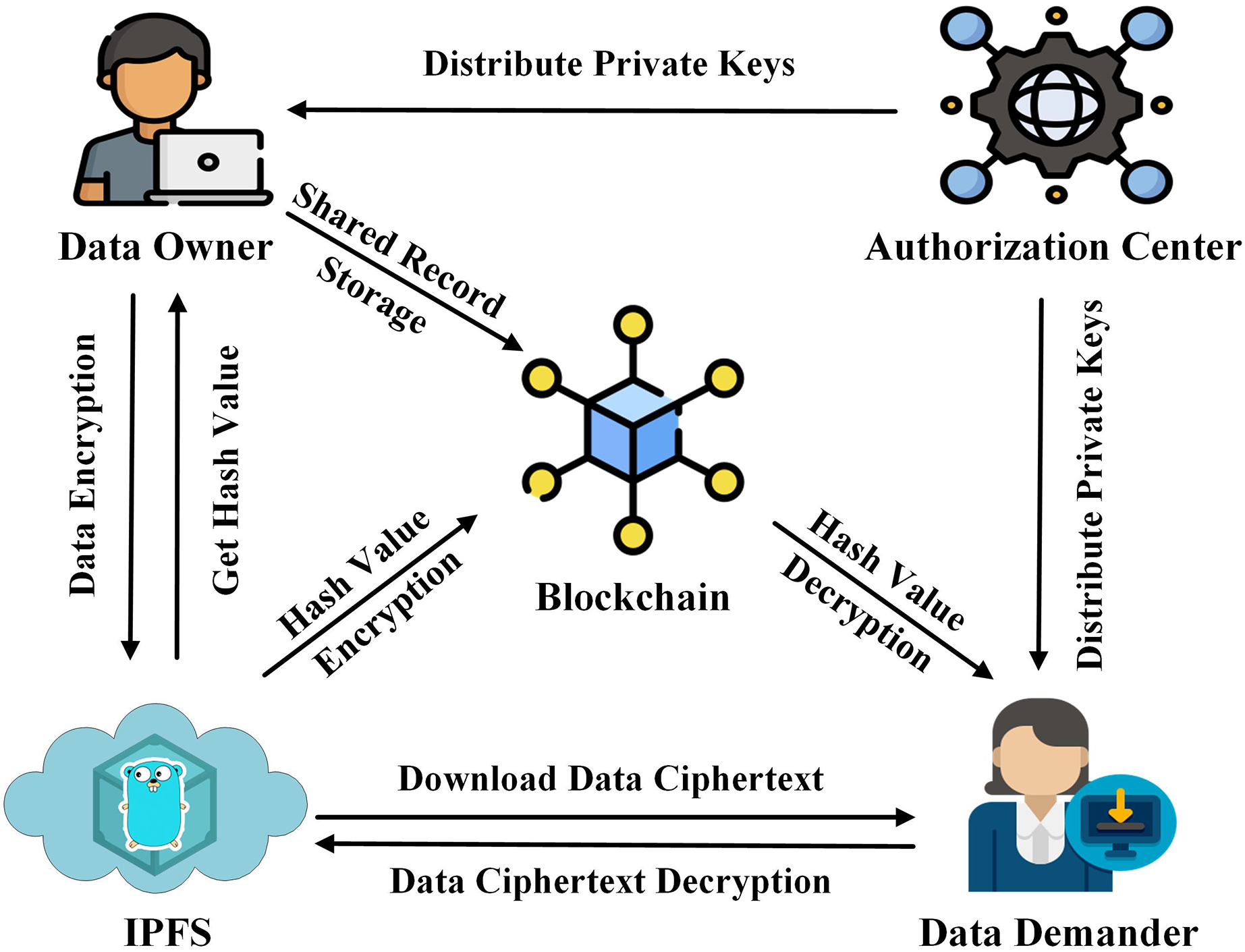
- Blockchain: Blockchain technology can be used to secure data sharing by providing a decentralized, immutable, and transparent way of storing and sharing data.